Defending Against Destructive Cyberattacks: Proactive Strategies for 2026
Learn proactive strategies against destructive cyberattacks: wipers, ransomware, and malware. Covers organizational resilience, detection, hardening endpoints, and recovery planning for 2026.
Destructive cyberattacks, including wipers, ransomware, and other malware designed to destroy data or render systems inoperable, pose a significant threat to organizations. While rare due to the risk of reprisal, their impact can be catastrophic, especially during geopolitical instability. This Q&A explores proactive measures—from organizational resilience to technical hardening—to help you prepare and defend against such attacks.
What exactly are destructive cyberattacks, and why are they particularly dangerous?
Destructive cyberattacks involve malware that intentionally destroys data, erases evidence of malicious activity, or manipulates systems to make them completely inoperable. Common examples include wipers (which overwrite data) and ransomware (which encrypts data for ransom). Unlike data theft, these attacks aim to cause permanent damage or disrupt operations. Threat actors use them as a cheap, easily deployable weapon during conflict or instability, when the risk of reprisal is considered acceptable. The danger lies in their ability to bring down critical infrastructure, halt business operations, and require extensive recovery efforts. Because they often target backup systems as well, recovery can be extremely challenging. While rare, these incidents heighten during geopolitical tensions, making preparation essential.
How can organizations build resilience beyond technical controls?
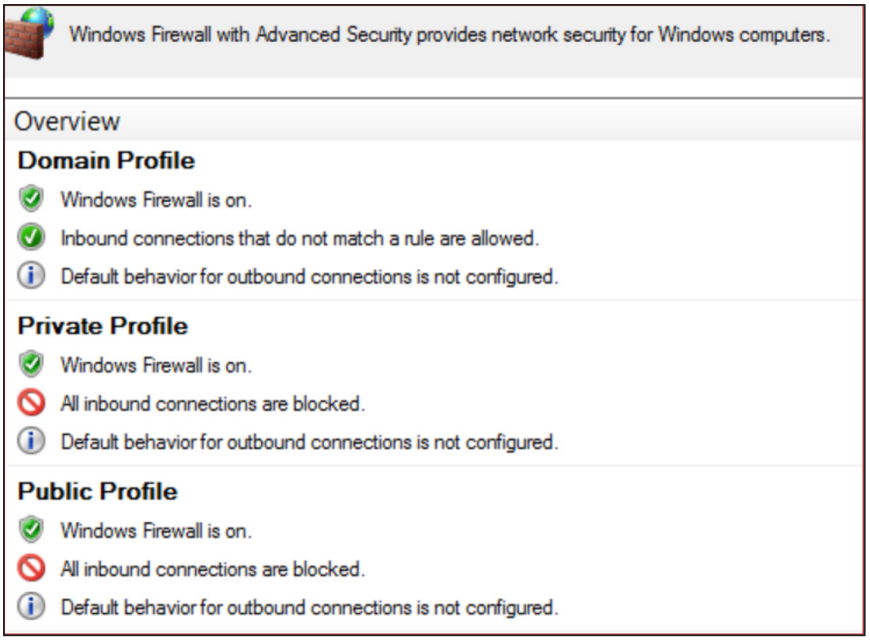
Organizational resilience goes beyond firewalls and antivirus. A living resilience posture includes two key components: out-of-band incident command and operational contingency plans. First, establish a decoupled communication platform that operates outside the corporate identity system. This ensures key stakeholders and third-party support can coordinate even if primary systems fail. Second, define baseline manual procedures for vital business functions. For example, how would you process orders or communicate with customers if servers are down? These plans should be rehearsed regularly. By integrating crisis preparation into security governance, organizations can react quickly and maintain continuity during restoration. This approach also helps detect attacks earlier, as manual checks may reveal anomalies automated tools miss.
What role do detection opportunities play in defending against destructive attacks?
Detection opportunities are supplementary monitoring methods that go beyond standard security tools. While endpoint and network tools use signatures and heuristics to detect known malware, custom detections focus on threat actor behavior rather than specific signatures. For instance, monitoring for unusual file deletion patterns or mass registry changes can signal a wiper attack in progress. Effective monitoring relies on baselines—understanding what is normal in your environment. Without baselines, you may miss subtle anomalies. These custom detections should trigger on divergence from normal patterns, such as unexpected PowerShell usage or large-scale data overwrites. The key is to correlate them with known threat tactics (e.g., reconnaissance, lateral movement) to catch attacks early, before they become destructive.
How can endpoint and MDM platforms be abused by attackers, and how should organizations respond?
Endpoint management and Mobile Device Management (MDM) platforms are powerful tools for IT teams, but attackers can abuse them to deploy destructive malware across devices simultaneously. For example, a threat actor who gains access to an MDM console can push a wiper to every connected device. To mitigate this, organizations should harden these platforms by enforcing strict access controls, requiring multi-factor authentication, and monitoring for anomalous administrator actions. Regularly review logs for bulk device commands or unauthorized configuration changes. Additionally, segment administrative access: use separate accounts for MDM administration and other tasks. If abuse occurs, have an immediate containment plan—such as disabling the MDM service or revoking certificates—to limit the blast radius. Training administrators to recognize signs of compromise is also vital.

What are some practical, scalable methods to protect against ransomware and wipers?
Scalable protections include regular backups stored offline or in a separate, immutable format (e.g., write-once media). Ensure backups are tested periodically for integrity. Implement least-privilege principles—users should only have access to files they need. Use application whitelisting to block unauthorized executables, especially from writable locations like temp folders. Deploy behavioral detection on endpoints to spot mass file encryption or deletion. For networks, segmentation limits lateral movement; if one segment is compromised, the attacker cannot easily reach critical servers. Outbound traffic filtering can block command-and-control communications. Finally, keep systems patched for known vulnerabilities. These methods are practical and can be gradually implemented based on risk assessment.
How does geopolitical instability increase the risk of destructive cyberattacks?
During conflict or political tension, cyberattacks become an attractive weapon because they are inexpensive and easy to deploy compared to kinetic warfare. Threat actors may target critical infrastructure, government networks, or private sector entities to cause strategic disruption. Destructive attacks in such contexts aim to damage enemy morale, disrupt supply chains, or erase data that supports operations. The risk of reprisal is weighed against potential gains; during instability, actors may be willing to accept higher risks. For organizations, this means elevated threat levels require increased vigilance, stricter access controls, and pre-established crisis communication plans. Staying informed about geopolitical developments can help prioritize defenses.
What should be included in a recovery plan after a destructive attack?
A recovery plan should start with assessing the damage: identifying which systems are affected and to what extent. Use offline backups to restore data, but first verify the backup chain is free from malware. Reimage systems from trusted media before restoring data. Implement manual procedures to maintain critical operations during restoration—for example, paper-based order processing. Communicate clearly with stakeholders using out-of-band channels. Document every step for post-incident analysis. The plan should also include testing the recovery process regularly, not just in theory. After recovery, review how the attack occurred and update security controls accordingly. A strong recovery plan shortens downtime and reduces overall impact.